The estimated reading time 8 minutes
Windows Fileserver Ressource Manager mehrere Dateiendungen per Powershell aus txt importieren
Da zur Zeit immer mehr RANSOMWARE auftaucht habe ich mich mit dem Thema beschäftigt die zahlreichen „verbotenen“ Endungen möglichst schnell in einen FSRM (Fileserver Ressource Manager) zu importieren (deutsch: Ressourcen-Manager für Dateiserver). Hierzu reicht ein kleiner Zweizeiler:
$extension = Get-Content .\endungen.txt Set-FsrmFileGroup -Name "Ransomware" -IncludePattern ($extension)
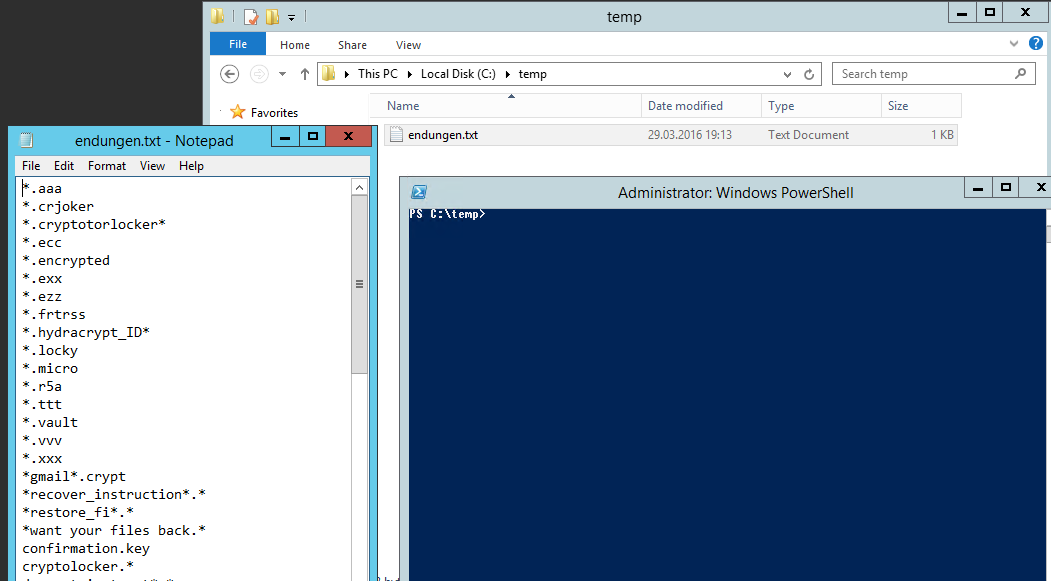
Ich habe vorab eine TXT-Datei erstellt und mit der Powershell in den Pfad der TXT gewechselt.
Hier meine Ransomware-Dateiendungen (Stand 17.05.2017).
UPDATE: unter https://www.bleib-virenfrei.de/ransomware/ kann man eine aktuelle Liste finden!
hier noch der direkte Link zur TXT Datei .
_secret_code.txt
_ryp
_Locky_recover_instructions.txt
_Locky_recover_instructions.bmp
_H_e_l_p_RECOVER_INSTRUCTIONS+*.txt
_H_e_l_p_RECOVER_INSTRUCTIONS*.txt
_H_e_l_p_RECOVER_INSTRUCTIONS*.png
_H_e_l_p_RECOVER_INSTRUCTIONS*.html
_how_recover.txt
_how_recover*.txt
_how_recover*.html
_HELP_instructions.txt
_HELP_instructions.bmp
_help_instruct*.*
_DECRYPT_INFO_*.html
_crypt
_*_HOWDO_text.html
zzzzzzzzzzzzzzzzzyyy
zycrypt.*
YOUR_FILES_ARE_LOCKED.txt
YOUR_FILES_ARE_ENCRYPTED.TXT
YOUR_FILES_ARE_ENCRYPTED.HTML
YOUR_FILES.url
YOUR_FILES.HTML
Your files encrypted by our friends !!! txt
Your files are locked !.txt
Your files are locked !!.txt
Your files are locked !!!.txt
Your files are locked !!!!.txt
YOUGOTHACKED.TXT
winclwp.jpg
wie_zum_Wiederherstellen_von_Dateien.txt
vault.txt
vault.key
vault.hta
UNLOCK_FILES_INSTRUCTIONS.txt
UNLOCK_FILES_INSTRUCTIONS.html
UnblockFiles.vbs
tox.html
strongcrypt.bmp
SIFRE_COZME_TALIMATI.html
SHTODELATVAM.txt
SECRETIDHERE.KEY
SECRET.KEY
Sarah_G@ausi.com___*
RESTORE_FILES_*.txt
RESTORE_FILES_*.*
restore_files.txt
restorefiles.txt
recovery_key.txt
RECOVERY_FILES.txt
recovery_file.txt
RECOVERY_FILE*.txt
recoveryfile*.txt
recovery+*.*
recoverfile*.txt
READ_THIS_TO_DECRYPT.html
Read_this_file.txt
READTHISNOW!!!.TXT
README_RECOVER_FILES_*.txt
README_RECOVER_FILES_*.png
README_RECOVER_FILES_*.html
README_HOW_TO_UNLOCK.TXT
README_HOW_TO_UNLOCK.HTML
readme_for_decrypt*.*
README_DECRYPT_UMBRE_ID_*.txt
README_DECRYPT_UMBRE_ID_*.jpg
README_DECRYPT_HYRDA_ID_*.txt
README_DECRYPT_HYDRA_ID_*.txt
readme_decrypt*.*
ReadDecryptFilesHere.txt
Read.txt
READ ME FOR DECRYPT.txt
Read Me (How Decrypt) !!!!.txt
READ IF YOU WANT YOUR FILES BACK.html
qwer2.html
qwer.html
pronk.txt
Payment_Instructions.jpg
paycrypt.bmp
oor.*.*
oor.*
oor*.
ONTSLEUTELINGS_INSTRUCTIES.html
OKSOWATHAPPENDTOYOURFILES.TXT
message.txt
MENSAGEM.txt
maxcrypt.bmp
last_chance.txt
KryptoLocker_README.txt
ISTRUZIONI_DECRITTAZIONE.html
INSTRUCTIONS_DE_DECRYPTAGE.html
Instructionaga.txt
INSTRUCCIONES_DESCIFRADO.TXT
INSTRUCCIONES_DESCIFRADO.html
INSTALL_TOR.URL
install_tor*.*
IMPORTANT.README
IMPORTANT READ ME.txt
IHAVEYOURSECRET.KEY
IAMREADYTOPAY.TXT
HOW_TO_UNLOCK_FILES_README_*.txt
how_to_unlock*.*
HOW_TO_RESTORE_FILES.html
How_to_restore_files.hta
How_To_Recover_Files.txt
how_to_recover*.*
How_to_decrypt_your_files.jpg
HOW_TO_DECRYPT_FILES.TXT
HOW_TO_DECRYPT.HTML
how_to_decrypt*.*
how_recover*.*
HOW_DECRYPT.URL
HOW_DECRYPT.TXT
HOW_DECRYPT.HTML
how_decrypt.gif
Howto_Restore_FILES.TXT
Howto_RESTORE_FILES.html
howto_restore*.*
HOWTO_RECOVER_FILES_*.*
howto_recover_file.txt
HowtoRESTORE_FILES.txt
howtodecryptaesfiles.txt
howtodecrypt*.*
howrecover+*.txt
HowDecrypt.txt
HowDecrypt.gif
HOW-TO-DECRYPT-FILES.HTML
how to get data.txt
how to decrypt*.*
How to decrypt your data.txt
How to decrypt LeChiffre files.html
HOW TO DECRYPT FILES.txt
HOW TO DECRYPT FILES.HTML
how to decrypt aes files.lnk
HELP_YOUR_FILES.TXT
HELP_YOUR_FILES.PNG
HELP_YOUR_FILES.html
help_your_file*.*
HELP_YOURFILES.HTML
HELP_TO_SAVE_FILES.txt
HELP_TO_SAVE_FILES.bmp
HELP_TO_DECRYPT_YOUR_FILES.txt
HELP_RESTORE_FILES_*.*
HELP_RESTORE_FILES.txt
help_restore*.*
help_recover_instructions+*.txt
help_recover_instructions*.txt
help_recover_instructions*.html
help_recover_instructions*.bmp
HELP_RECOVER_FILES.txt
help_recover*.*
help_instructions.*
help_file_*.*
help_decrypt_your_files.html
HELP_DECRYPT.URL
Help_Decrypt.txt
HELP_DECRYPT.PNG
HELP_DECRYPT.lnk
HELP_DECRYPT.HTML
help_decrypt*.*
HELPDECYPRT_YOUR_FILES.HTML
HELPDECRYPT.TXT
help-file-decrypt.enc
Help Decrypt.html
HELLOTHERE.TXT
Hacked_Read_me_to_decrypt_files.html
GetYouFiles.txt
FILES_BACK.txt
FILESAREGONE.TXT
File Decrypt Help.html
exit.hhr.obleep
ENTSCHLUSSELN_HINWEISE.html
enigma_encr.txt
enigma.hta
enc_files.txt
enc_files*
encryptor_raas_readme_liesmich.txt
encryptor_raas_readme_liesmich*
email-salazar_slytherin10@yahoo.com.ver-*.id-*-*.randomname-*
de_crypt_readme.txt
de_crypt_readme.html
de_crypt_readme.bmp
de_crypt_readme.*
DESIFROVANI_POKYNY.html
default432643264.jpg
default32643264.bmp
decypt_your_files.html
DECRYPT_YOUR_FILES.txt
DECRYPT_YOUR_FILES.HTML
DECRYPT_ReadMe1.TXT
DECRYPT_Readme.TXT.ReadMe
DECRYPT_ReadMe.TXT
DECRYPT_ReadMe*
DECRYPT_INSTRUCTIONS.TXT
DECRYPT_INSTRUCTIONS.html
DECRYPT_INSTRUCTION.URL
DECRYPT_INSTRUCTION.TXT
DECRYPT_INSTRUCTION.HTML
decrypt_instruct*.*
DECRYPTION_HOWTO.Notepad
DecryptAllFiles.txt
DecryptAllFiles*.txt
DecryptAllFiles*
decrypt-instruct*.*
Decrypt All Files *.bmp
cryptolocker.*
cryptinfo.txt
crjoker.html
confirmation.key
Como descriptografar seus arquivos.txt
Comment débloquer mes fichiers.txt
Coin.Locker.txt
BUYUNLOCKCODE.txt
BUYUNLOCKCODE
BitCryptorFileList.txt
ATTENTION!!!.txt
AllFilesAreLocked*.bmp
About_Files.txt
4-14-2016-INFECTION.TXT
*_ryp
*_recover_*.*
*_nullbyte*
*_HOWDO_text.html
*_HOWDO_text.bmp
*_HELP_instructions.html
*_help_instruct*.*
*warning-!!*.*
*want your files back.*
*ukr.net*
*restore_fi*.*
*recover}-*.*
*recover_instruction*.*
*rec0ver*.*
*qq_com*
*maestro@pizzacrypts.info
*keemail.me*
*install_tor*.*
*how_to_recover*.*
*help_restore*.*
*gmail*.crypt
*files_are_encrypted.*
*dxxd
*DECRYPT_INSTRUCTION*
*decryptmyfiles*.*
*decrypt your file*.*
*decrypt my file*.*
*decipher*
*cpyt*
*cerber2
*@india.com*
*@gmail_com_*
*.암호화ë¨
*.å·²åŠ å¯†
*.~HL*
*.{CRYPTENDBLACKDC}
*._ryp
*._AiraCropEncrypted!
*.zzz
*.zypto*
*.zyklon
*.Zimbra
*.zepto
*.zcrypt
*.zc3791
*.Z81928819
*.YTBL
*.Yakes
*.xyz
*.xxx
*.xtbl
*.xrtn
*.XRNT
*.xort
*.xorist
*.xcrypt
*.windows10
*.Where_my_files.txt
*.wflx
*.vvv
*.vscrypt
*.venusp
*.Venusf
*.vault
*.unbrecrypt_ID_*
*.unavailable
*.tzu
*.ttt
*.trun
*.troyancoder@qq_com
*.toxcrypt
*.szf
*.surprise
*.SUPERCRYPT
*.sshxkej
*.sport
*.Silent
*.shino
*.SecureCrypted
*.SecureCrypte
*.scl
*.sanction
*.ryp
*.rtyrtyrty
*.RSplited
*.RSNSlocked
*.RRK
*.rokku
*.remind
*.relock@qq_com
*.rekt
*.Read_Me.Txt
*.RDM
*.razy
*.RADAMANT
*.RAD
*.R5A
*.R4A
*.R16M01D05
*.pzdc
*.purge
*.POSHKODER
*.pornoransom
*.porno.pornoransom
*.porno
*.PoAr2w
*.plauge17
*.pizda@qq_com
*.pdcr
*.payransom
*.paymst
*.payms
*.payfornature@india.com.crypted
*.paybtcs
*.padcrypt
*.p5tkjw
*.oshit
*.oplata@qq_com
*.oor
*.only-we_can-help_you
*.one-we_can-help_you
*.OMG!
*.odin
*.odcodc
*.nochance
*.neitrino
*.nalog@qq_com
*.micro
*.magic_software_syndicate
*.magic
*.LOL!
*.locky
*.locked
*.legion
*.LeChiffre
*.krypted
*.kratos
*.kraken
*.korrektor
*.kkk
*.kimcilware.locked
*.kimcilware
*.KEYZ.KEYH0LES
*.KEYZ
*.KEYHOLES
*.KEYH0LES
*.keybtc@inbox_com
*.keybtc@inbox
*.justbtcwillhelpyou
*.iwanthelpuuu
*.isis
*.infected
*.hydracrypt_ID_*
*.hydracrypt_ID*
*.How_To_Get_Back.txt
*.How_To_Decrypt.txt
*.herbst
*.helpdecrypt@ukr_net
*.helpdecrypt@ukr.net
*.helpdecrypt@ukr*.net
*.heisenberg
*.hb15
*.ha3
*.h3ll
*.gws.porno
*.gws
*.gruzin@qq_com
*.good
*.fun
*.fuckyourdata
*.fucked
*.fuck
*.frtrss
*.fileiscryptedhard
*.fantom
*.ezz
*.exx
*.evil
*.epic
*.enigma
*.encryptedRSA
*.encryptedped
*.encryptedAES
*.encrypted.locked
*.Encrypted
*.encrypt
*.encoderpass
*.EnCiPhErEd
*.encedRSA
*.eclr
*.ecc
*.dyatel@qq_com
*.domino
*.ded
*.da_vinci_code
*.darkness
*.czvxce
*.CTBL2
*.ctbl
*.CTB2
*.CrySiS
*.crypz
*.cryptz
*.crypttt
*.cryptowall
*.CryptoTorLocker2015!
*.cryptotorlocker*
*.cryptolocker
*.crypto
*.crypted
*.crypt38
*.crypt1
*.crypt
*.cryp1
*.cry
*.CRRRT
*.crptrgr
*.crjoker
*.crjocker
*.cripttt
*.criptokod
*.criptiko
*.crinf
*.crime
*.cRh8
*.crashed
*.coverton
*.Contact_Here_To_Recover_Your_Files.txt
*.code
*.clf
*.chifrator@qq_com
*.cerber3
*.cerber2
*.cerber
*.CCCRRRPPP
*.ccc
*.cbf
*.cawwcca
*.canihelpyou
*.C0rp0r@c@0Xr@
*.btcbtcbtc
*.btc.kkk.fun.gws
*.btc-help-you
*.btc
*.breaking_bad
*.breaking bad
*.bloccato
*.blocatto
*.bloc
*.bleepYourFiles
*.bleep
*.bitstak
*.better_call_saul
*.bart.zip
*.bart
*.b5c6
*.axx
*.asdasdasd
*.ap19
*.amba
*.akaibvn
*.aga
*.AFD
*.AES256
*.abc
*.aaa
*.a5zfn
*.a19
*.8lock8
*.7z.encrypted
*.7h9r
*.777
*.73i87A
*.6FKR8d
*.31392E30362E32303136_*
*.31342E30362E32303136*
*.1999
*.0x0
*.*obleep
*.*nochance
*.*locked
*.*kraken
*.*kb15
*.*exx
*.*darkness
*.*crypto
*.*cry
*-recover-*.*
*+recover+*.*
*!recover!*.*
*!DMAlock*
$RECYCLE.BIN.{*-*-*-*}
# DECRYPT MY FILES #.vbs
# DECRYPT MY FILES #.txt
# DECRYPT MY FILES #.html
!Where_are_my_files!.html
!satana!.txt
!Recovery_*.txt
!readme.*
!DMALOCK3.0*
!!!README!!!*.rtf
!!!-WARNING-!!!.txt
!!!-WARNING-!!!.html
Um nun diese Infos in den FSRM zu importieren die Endungen in ein TXT File kopieren.
In meinen Fall liegt dieses unter „C:\temp\endungen.txt“:
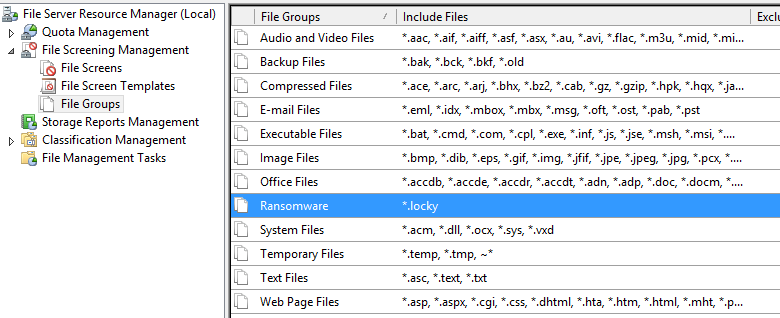
Ich habe bereits davor eine Dateigruppe (Filegroup) mit dem Namen „Ransomware“ erstellt.
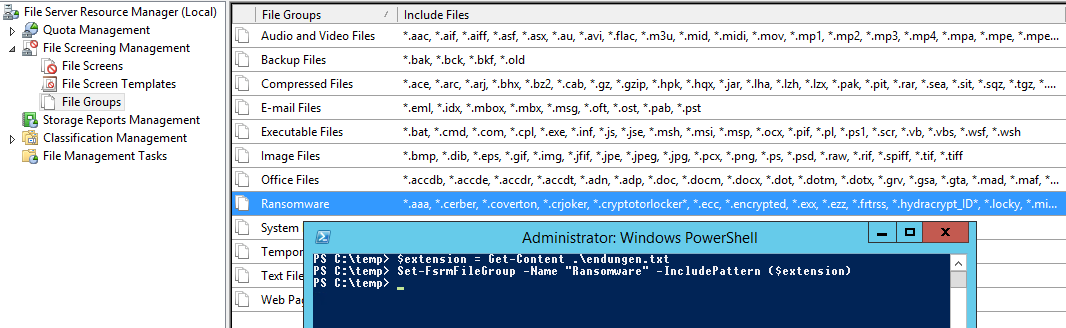
Um dieser nun die restlichen Endungen per Powershell hinzuzufügen muss folgender Befehl eingegeben werden.
$extension = Get-Content .\endungen.txt Set-FsrmFileGroup -Name "Ransomware" -IncludePattern ($extension)
Viel Spaß beim Testen.

Hi,
heute die Bekanntschaft mit der Endung *.orion._ gemacht. Weder in der Liste noch auf bleib-virenfrei.de zu finden.
Hi,
sehr informativer Beitrag.
Habe aktuell einen Virus-Befall gehabt, dessen Änderungen bei nahezu jeder Datei gewechselt haben… hier gíbt es einen Screenshot zu den Endungen…
https://www.administrator.de/wissen/cryptolocker-wechselnden-datei-endungen-331028.html
Gibt es eigentlich einen Powershell-Befehl um die Liste zu ergänzen, statt komplett zu überschreiben?
Es ist so das ich gerne diese Liste nehmen würde und noch weitere aus dem Netz. Zur Zeit müsste ich beide Listen erst manuell in einer txt zusammenfassen. Schöner wäre es wenn ich kurz nacheinander beide listen per befehl lade ohne das er die vorherige wieder überschreibt.
Ich teste das und versuche das in den Artikel einfließen zu lassen.
Hallo Benni,
ich habe nun einen weiteren Artikel dazu verfasst. Siehe Teil 2 https://blog.it-koehler.com/Archive/1335
Versuchs mal damit.
Viele Grüße
*.hta und *.RMCM1 könnte noch aufgenommen werden.
Hier gibt es weitere Informationen dazu:
https://www.mysonicwall.com/Emails.aspx?utmhn=THREAT_PROTECTION&utmdt=THREAT_PROTECTION_MESSAGEURL&utmp=THREAT_PROTECTION_MESSAGEURL&tu=aHR0cHM6Ly93d3cubXlzb25pY3dhbGwuY29tL3NvbmljYWxlcnQvc2VhcmNocmVzdWx0cy5hc3B4P2V2PWFydGljbGUmaWQ9OTk2
Wie kann man den die Liste unter Server 2008 hinzufügen?
Danke für die Antwort
Hallo Kwirch,
leider sind die fsrm cmdlets nicht auf Windows Server 2008R2 verfügbar.
https://technet.microsoft.com/en-us/library/jj900651(v=wps.620).aspx
Mit 2008R2 lässt sich das hinzufügen über eine EXE realisieren
>>>>>> filescrn Filegroup Add /Filegroup:“CryptoWall File Monitor“ /Members:“*DECRYPT*“ <<<<<<< Da hier eine foreach Schleife nicht funktioniert (es gibt kein "append"), gibt es meines Erachtens nur eine einzige Möglichkeit das ganze halbwegs automatisiert zu machen >>>>> filescrn filegroup export /file:C:\temp\filegroups.xml /filegroup:“Crypto“ <<<<<<< Der Befehl exportiert die komplette Filegruppe und man könnte mit einer Excel Funktion die Endungen in die XML einbauen. Ist war nicht sonderlich professionell aber würde eventuell funktionieren. hier noch der Link zur MS Referenz filescrn https://technet.microsoft.com/de-de/library/cc788082(v=ws.10).aspx
Bei Unklarheiten melden.
*.zzzzz
gibt es jetzt auch schon
Vielen Dank. Habe ich ebenfalls gefunden. Ist nun in der Liste drin.
Bitte *.thor aufnehmen!
danke für den Hinweis ist nun drin!